With IP based authentication, you will need to obtain the IP address of the host from the trunk provider.
Follow the steps below to setup a PEER based IP authenticated trunk:
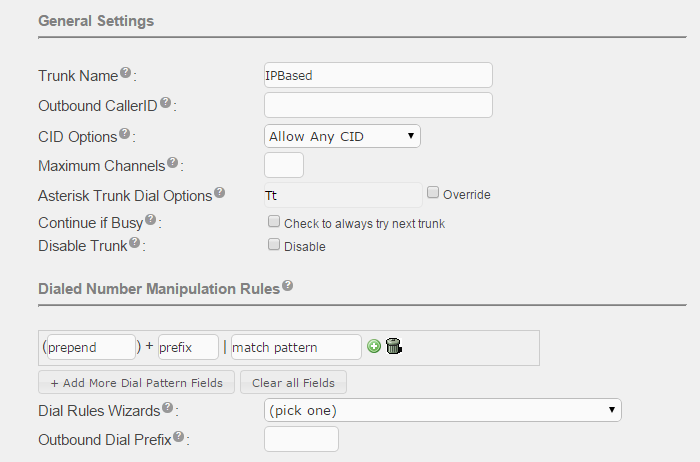
Enter the Trunk Name, this is the name used to referenced the trunk, for example in the Inbound and Outbound Route pages.
(See Adding SIP Trunks for information on the other fields in this section.)
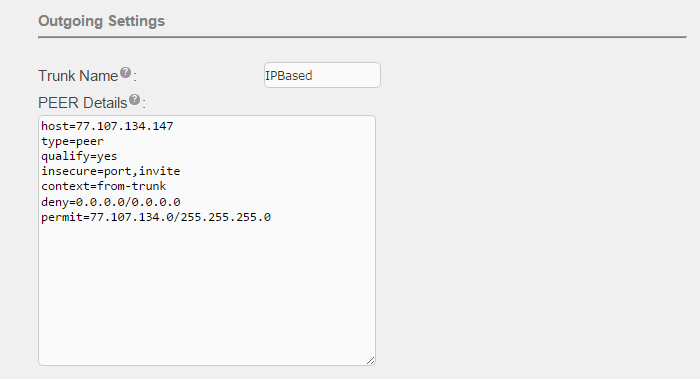
Enter the Trunk Name (DO NOT use spaces). This name will appear in log files.
For PEER Details, these are the recommended settings:
| Parameter | Value | Description |
|---|---|---|
| host | xxx.xxx.xxx.xxx | IP address of the SIP trunk provider's server |
| type | peer | The supported values are: peer, user, friend. Friend is both a peer and user. |
| context | from-trunk |
"from-trunk" means that incoming calls from this trunk will be treated as if they are coming from an outside line, and will be routed using the rules that you setup in the Inbound Routes page. "from-internal" means that incoming calls from this trunk will be treated as if they were made by an internal phone, and will be routed directly to an extension number, a feature code, or through the outbound routes page. Generally, you use "from-trunk" when routing calls from an outside source and "from-internal" for trunks that tie two trusted systems together. |
| qualify | yes | "yes" means to periodically send a request that the other system identify itself. If there is no answer within 2 seconds, your system will assume that the other system is down and stop sending calls to the system until the system responds. Instead of "yes," you can also put a number, in miliseconds. For example, qualify=3000 means that your system will wait 3 seconds for a response, instead of 2 seconds. |
| insecure | port,invite |
"port" means to accept incoming calls even if they come from a port other than the one where calls are expected to come from. "invite" means to accept incoming calls even if they are not accompanied by the proper username and password. Most ITSP's require this line. If only one is used, the comma separating them is omitted. |
| deny | 0.0.0.0/0.0.0.0 | [Optional] For added security, include "deny" and "permit" to limit access based on IP address. |
| permit | xxx.xxx.xxx.0/255.255.255.0 | [Optional] Allow access only to the specified IP subnet. |
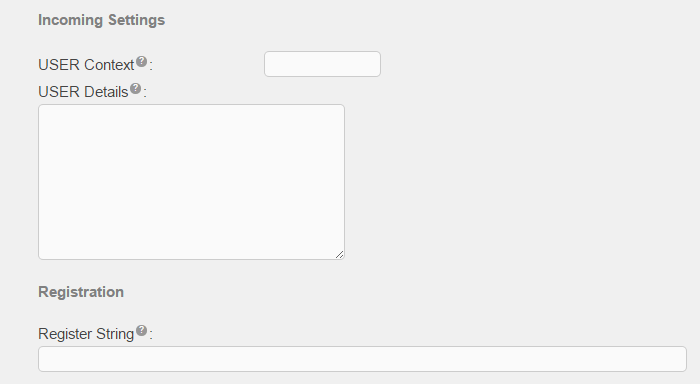
Leave the USER Context and USER Details blank
Leave the Register String blank.